Crypto stealth addresses, explained
The purpose of crypto stealth addresses is to enable privacy for each transaction, concealing the recipient’s identity and transaction history.
Crypto stealth addresses are a privacy-enhancing feature in blockchain technology that lets users receive money anonymously. Unlike conventional public addresses, stealth addresses provide distinct, one-time addresses for every transaction. The recipient’s actual address is kept secret when a sender transfers funds using a stealth address; the transaction is broadcast to the network.
The recipient does not directly generate a private key from the stealth address; the wallet is designed to identify incoming transactions. It then utilizes the private key associated with the recipient’s public address to facilitate the recognition and processing of these transactions. This process allows the recipient to access and control the received funds without exposing their primary address.
As a result, the privacy of cryptocurrency transactions is significantly increased, shielding users from potential monitoring or examination of their financial activity. Crypto stealth addresses support the continued development of private and secure transactions within the blockchain ecosystem by adding additional protection.
Monero (XMR) is a prominent example of a cryptocurrency that uses stealth addresses. It uses a variety of features, including ring signatures and stealth addresses, to provide its users with increased privacy and anonymity. The recipient’s stealth address is used during a Monero transaction, making it challenging for outside observers to connect the sender, recipient and transaction amounts.
Stealth addresses vs. regular wallet addresses
Stealth addresses offer improved transaction privacy with unique, one-time addresses, whereas regular wallet addresses lack such privacy measures and are frequently static.
Stealth addresses resemble standard cryptocurrency addresses in appearance, typically consisting of a string of characters and digits. The key differences, though, are in their one-time usage and the cryptographic methods used to obfuscate the connection between the recipient’s real address and the stealth address.
In contrast, when utilizing traditional wallet addresses, the repetition of a single address for multiple transactions allows for the mapping of users’ financial activities. Due to the possibility of revealing sensitive information, this practice violates privacy by enabling third parties to monitor and examine transaction histories.
Moreover, adversaries could use this pattern to identify sources of income, spending patterns and general financial behavior. Furthermore, address reuse raises the possibility of several attacks, such as attempts at deanonymization and the possible exposure of users to malevolent organizations.
How do stealth addresses work?
Crypto stealth addresses enhance privacy by creating unique addresses for each transaction, allowing only the intended recipient to access and identify the funds.
To understand how stealth addresses can be used, let’s walk through an example: Bob and Alice are two individuals using a hypothetical cryptocurrency. They decided to use stealth addresses in an attempt to increase their privacy. These cryptographic constructs offer an additional degree of anonymity, which creates distinct, one-time addresses for every transaction.
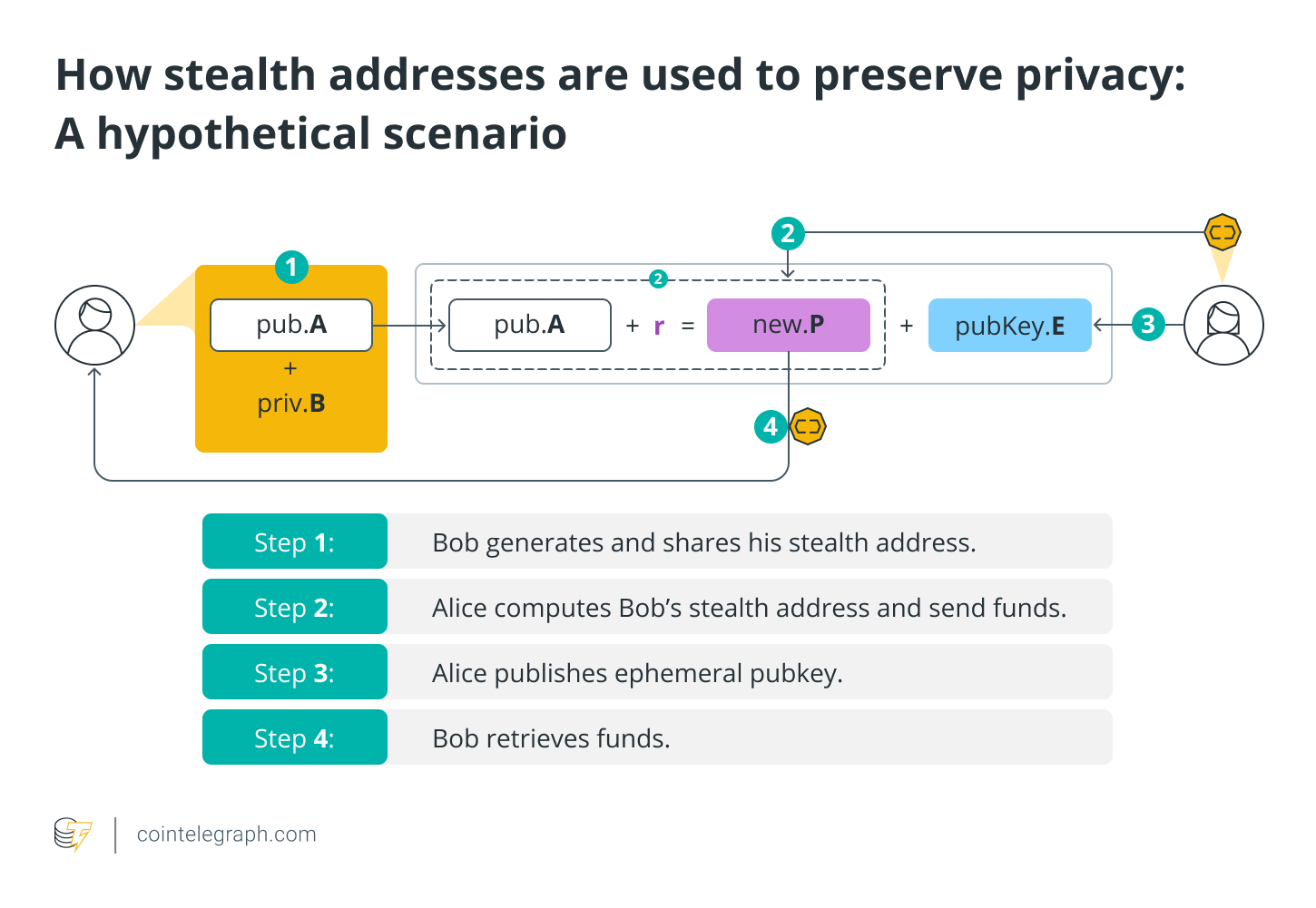
Step 1: Bob generates and shares his stealth address
Bob creates two addresses (let’s call them A and B), but only shares A publicly while keeping the private address B secret. This combo is his new “stealth address,” which is an apparently random series of characters exclusive to this transaction. Together, the pair (A, B) form the stealth address that Bob uses to receive funds.
To complete the transaction, Bob provides Alice, the sender, with the generated stealth address (public), an essential piece of information that Alice will need to create Bob’s stealth address.
Step 2: Alice computes Bob’s stealth address and sends funds
Alice performed cryptographic computations using Bob’s public stealth address (A) and the random number (r) to create a brand new address (let’s call it P). A distinct, one-time stealth address (temporary) is generated especially for this transaction as a consequence of this computation. Alice sends the funds to this address (P), enhancing the privacy of the transaction.
Step 3: Alice publishes ephemeral pubkey
Alice posts extra cryptographic information called ephemeral pubkey (let’s call it E) on the blockchain, which Bob needs to locate and claim the assets. An ephemeral public key is a temporary public key generated for a specific cryptographic transaction. This pubkey is not directly tied to the user’s long-term public address.
Step 4: Bob retrieves funds
Bob keeps an eye on the network for any transactions involving his stealth address. When he sees Alice’s transaction to P, he uses his secret addresses (A and B) and the ephemeral public key (E) to figure out the original secret number (r). The use of ephemeral pubkeys makes it challenging for outside parties to track down and connect numerous transactions to a single user, even though they are visible on the blockchain.
Throughout the process, the Diffie-Hellman key exchange protocol is employed, allowing Bob and Alice to create a shared secret over an insecure communication channel. This shared secret is combined with Bob’s private key in stealth address generation to produce an unlinkable and distinct destination address. This procedure makes sure that different transactions involving the same recipient stay cryptographically distinct.
Advantages and disadvantages of stealth addresses
Stealth addresses offer heightened transaction privacy but may introduce complexity and slower processing times compared to regular wallet addresses.
Advantages of stealth addresses
There are several benefits to using a stealth address, including enhanced security and privacy in cryptocurrency transactions. As every transaction uses a distinct, one-time stealth address, stealth addresses support user anonymity by making it difficult for outside parties to track the movement of funds on the blockchain.
Stealth addresses also lessen the chance of address reuse, which lessens the possibility of transaction linkability and protects the privacy of users’ financial activity. For cryptocurrencies to remain fungible — that is, for one unit to be identical to another — this increased privacy protection is especially crucial.
Disadvantages of stealth addresses
Despite their privacy benefits, stealth addresses are not without drawbacks. A significant obstacle is the possible intricacy of their implementation, which may cause user errors and complicate wallet software. Transaction processing times may be slower than for traditional transactions due to the extra computational steps needed to create and retrieve funds from stealth addresses.
Furthermore, stealth addresses have not been widely adopted by all cryptocurrencies, which limits their usefulness in some ecosystems. Like with any new technology, it is essential to train users to use stealth addresses correctly to maximize their advantages and minimize any potential concerns.